Estimated Reading Time: 7 Minutes
2020 created a perfect storm for cyber-crime. A worldwide pandemic, combined with a massive shift to remote work, provided a perfect environment for criminals to exploit employees and their organizations. From board rooms to company all hands meetings, business leaders increasingly describe the situation as a world at war, pitting cyber criminals against legitimate businesses, governments, and institutions.
Unfortunately, MSPs are on the front lines of this war.
Now more than ever, cyber criminals view MSPs as a linchpin in their attacks: a breach of an MSP gives an attacker downstream access to literally dozens of SMB and enterprise clients and thousands of users. Over the past two years, the number of MSPs victimized by data breaches and security incidents has mushroomed. In many of these attacks, the very tools that MSPs use to manage thousands of users, such as remote monitoring and management (RMM) software programs, are leveraged and turned against the clients and their users. For example, in the latest Kaseya VSA breach, a vulnerability in Kaseya’s RMM tool led to breaches at dozens of MSPs and hundreds of downstream clients.
With such a widespread crisis, it is obvious that every MSP should beef up their investments in cyber security technologies, services, and best practices, both for their own organizations and their clients. Additional cyber liability insurance coverage, third-party pen-testing, technology upgrades, and business continuity improvements are all on deck and will yield big dividends for vigilant and forward looking MSPs.
Importantly, to judge the return on investment for additional cyber security measures, MSPs should understand the costs and consequences of inaction. It is vital for MSP leaders to understand the various costs of a security breach or incident.
In this blog post, we explore the eight biggest cost areas an MSP will face if they fall prey to a cyber-attack. These insights were gathered through confidential interviews with MSP business leaders and cyber liability insurance executives. For obvious reasons, the names of the specific companies have been omitted. Nevertheless, the learnings and insights shared in this blog post come from the frontlines in the fight against cyber-crime.
Lost Business and Client Damages
The biggest cost of a cyber security incident is usually business disruption and downtime. For instance, in a ransomware attack, computers and servers go offline, preventing companies from conducting normal business operations. In the recent Colonial Pipeline ransomware attack, the largest fuel pipeline in the United States was shut down for several days, causing wholesale fuel shortages, consumer hoarding at the pump, and widespread shortages at the retail level. After a few days of downtime, retail fuel prices spiked to their highest levels seen in the past decade. In another incident, the JBS Foods ransomware attack shut down five of the largest meat packing plants in the United States, causing similar shortages and consumer panic.
For most MSPs, if their client’s get impacted by a data breach or security incident, it likely will not make national news. Nevertheless, the costs can add up quickly. According to a 2020 study conducted by IBM and the Ponemon Institute, 39.4% of the economic damages from a security breach arise from downtime, business disruptions, and lost revenue. If an MSP’s client gets hit with ransomware, e-commerce sites go down, websites are taken offline, sales orders can’t be booked, trucks don’t roll, and customers are often left in the dark without service or support. In these circumstances, the clients, or more commonly the clients’ insurance carriers, will sue the MSP and seek financial relief.
When all is said and done, client business disruption is usually the largest cost, especially if the MSP itself was the nexus of the attack. Fortunately, these costs are usually covered under an MSP’s cyber liability policy.
Legal Fees
There is no shortage of legal work stemming from cyber security incidents. The legal costs really add up since every impacted party and their insurance company will sue to seek relief or defend themselves. After an incident, MSP leaders will find themselves in damage control mode 24/7. Instead of working with clients on novel technology challenges, hundreds of hours will now need to be spent with teams of lawyers wrangling over damages.
Most of the legal costs are borne by the insurance carriers after an incident, but countless hours of leadership time will nevertheless be spent on meeting with lawyers instead of helping clients. Most commonly, the process of subrogation kicks in, and the client’s insurance carriers and their lawyers will seek damages and relief from the MSP’s insurance carriers. So again, these costs are insurable provided the right levels of coverage are in place.
Response, Remediation, and Labor Costs
Generally, when there is a breach, data theft, or ransomware attack, massive amounts of technician time are needed to get things restored and back to normal. Even when ransoms are quickly paid and encryption keys are in hand, it is an all-hands-on deck process to recover clients from a ransomware infection. Not surprisingly, it is often a race against the clock. Time is money. So, extra outside service providers are often needed to help in the crisis and overtime costs go through the roof.
Like with legal costs and client damages, the extra labor costs will be covered and reimbursed by the carrier. But be forewarned, normal salary and wages of technical staff working on a ransomware recovery, for instance, will not be reimbursed. Even if 90% of staff time is dedicated to a security incident response, only the overtime and outside vendor costs will be reimbursed.
Emergency Technology and Infrastructure Needs
When responding to a security incident, an MSP will often have to make emergency procurement of hardware and software. For instance, in a ransomware response, an MSP will commonly have to purchase lots of server hardware to do rapid restores of client backups to get things back to normal as quickly as possible. These purchases will often be made quickly and at top dollar. These investments will usually be covered by insurance.
Ransomware Payments
Ransom payments to cyber criminals are unfortunately all too common. Sometimes, the cyber criminals compromise an MSP’s or client backups. In other cases, the cyber criminals may have exfiltrated data and threaten the release of the data if the ransom isn’t paid. And in other cases, sometimes paying the ransom is the quickest way to restore full operations, if the backup provider is swamped or lacks the capacity for quick restores in the cloud or through data exports. While the ransomware payments made by large companies often make headlines, the good news is that ransom payments are usually the smallest tangible cost in a data breach or incident.
There are other considerations with ransom payments as well. In many circumstances, companies paying a ransom may be unaware of the identities or physical locations of the cyber criminals. The U.S. federal government has strict prohibitions against providing financial assistance to sanctioned individuals or jurisdictions. Paying ransoms may unwittingly expose companies to civil liabilities or legal issues stemming from the provision of financial resources to adversaries of the United States. MSPs are encouraged to study the relevant guidance provided by the U.S. Treasury Department on this topic
https://home.treasury.gov/system/files/126/ofac_ransomware_advisory_10012020_1.pdf
Client Attrition and Reputational Damage
As time goes on after an incident, it becomes harder to calculate the precise cost of an incident. This is especially the case with client attrition. If an MSP falls prey to an attack, invariably the company will suffer reputational damage and client losses. Reputational damage can make winning new clients even harder. Calculating these costs can become murky. Did the client leave because of the incident, or was this just the last straw in a fractured business relationship? Did the client leave specifically because the MSP got breached or not? Is growth plateauing because of our sales performance or our damaged reputation?
These questions are always hard to answer and therefore, these sorts of costs usually go uncovered. The MSP bears these costs directly and the real economic costs can slowly unfold over months and years. The damage may well be incalculable. Fortunately, if an MSP responds professionally and quickly to a security incident, most clients are loyal and forgiving, especially if they are made whole for any hard costs or business losses associated with the incident. In surveying the market, many MSPs emerge from cyber security incidents stronger, wiser, and ready to double-down with a security-first approach going forward. No one wants to learn business lessons the hard way, but there are lots of success stories of MSPs surviving and thriving after a security incident.
Distraction, Disruption, and Employee Losses
Security incidents take a human toll as well. For most MSPs, the founder’s net worth and pride are 100% invested in their business. Suffering an attack can take an unbearable emotional and psychological toll. No matter how someone responds in the heat of the crisis, a cyber security incident may mean long hours and sleepless nights for weeks and months on end for everyone involved. Frontline staff will commonly work nights and weekends in the first days and weeks after an incident. The increased workloads can go on for on months. Stress, anxiety, and extra work can push teams to their breaking points.
Company owners, leaders and staff need to be mindful of the physical and emotional costs of a cyber security crisis. The best performing teams bring in outside advisors, vendors, and service providers to lighten the load and keep an even keel. For teams to weather the crisis, balance and realistic expectations need to kick in quickly. Everyone from the CEO on down, should get enough sleep, nourishment, and rest as the crisis unfolds. While people will willingly sacrifice in a crisis, it is also vital to remember the needs of spouses, partners and family members.
Post-event, Technology Upgrades and Investments
Lastly, MSPs will have a lot of costs battling back from a security incident, with technology improvements and additional costly upgrades. Commonly, MSPs will switch out whole vendor solutions after a breach if a vendor or their product contributed to the crisis. Over the years, we have seen PSA, RMM, AV, firewall, and backup vendors switched out completely, if they were weighed in the balance and found wanting.
In these cases, the MSP will often face one-time switching costs and higher ongoing licensing costs to arrive at a higher level of protection and reliable performance. Again, these costs can really add up over time. However, additional investments should have a strong ROI, because they will help the MSP staff sleep again, protect the MSP and client networks, and ensure the successful delivery of their managed services. Right or wrong, MSP leadership will bear nearly any expense to get back to a highly secure and reliable operation.
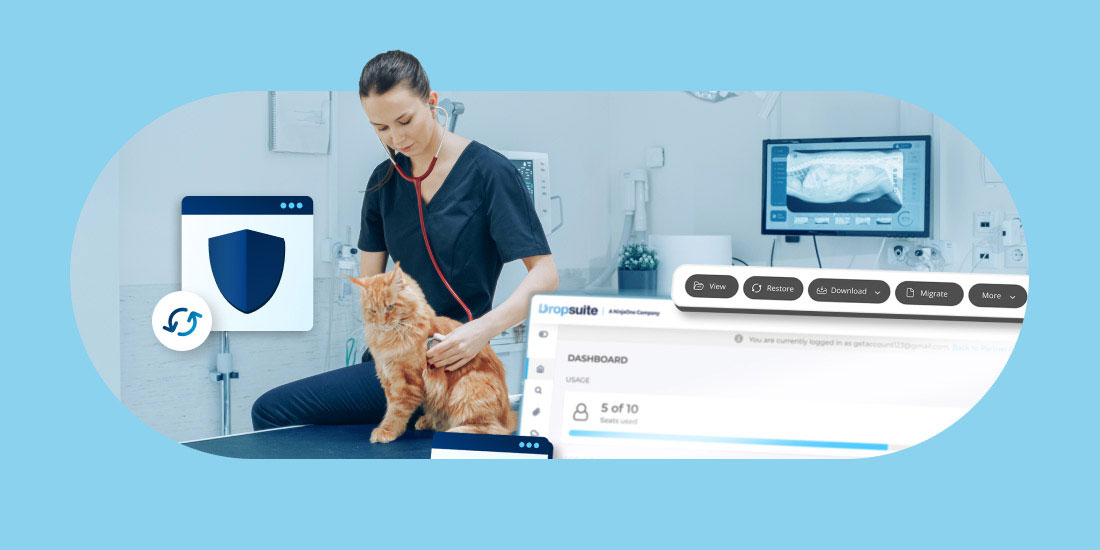
Dropsuite helps MSPs battle cyber criminals by backing up and protecting cloud data from Microsoft 365 and Google Workspace, giving MSPs a last line of defense during and after a data breach or security incident.