Estimated Reading Time: 4 Minutes
Managed Service Providers (MSPs) are at the forefront of IT innovation, helping businesses across industries manage their technology needs. Yet, with great responsibility comes great challenges.
This article explores the top four challenges MSPs face today, supported by recent studies and statistics, and explains how backup and archiving technologies can be leveraged to overcome them.
Challenge #1: Accidental Deletions
Human error is the leading cause of data loss globally. A 2023 report by Verizon’s Data Breach Investigations Report (DBIR) highlighted that 82% of breaches involved the human element, including errors, misuse, and social engineering. For MSPs managing critical client data, accidental deletions can result in downtime, legal repercussions, and financial loss.
Common Scenarios:
- Accidental File Deletions: Employees unintentionally delete critical files or overwrite existing data.
- Data Sprawl: Users store files in unapproved locations, making recovery more complex.
- Unsecured Devices: According to Kensington, 70 million smartphones are lost annually, with only 7% recovered. Business data on these devices often becomes inaccessible or compromised.
- Poor Offboarding: A recent study revealed that 63% of businesses experienced data loss due to inadequate employee offboarding processes.
How Backup and Archiving Help:
- Automated backup ensures that all data is securely stored and recoverable.
- Long-term archiving preserves historical data, ensuring compliance and retrieval even years later.
Challenge #2: Scaling with Limited Resources
As the global managed services market is projected to grow at a CAGR of 13.6%, reaching $731.08 billion by 2030, MSPs face pressure to scale efficiently, often requiring the right Managed Service Provider software to streamline operations. Smaller MSPs, in particular, struggle to expand services without overwhelming resources or compromising service quality.
Key Barriers:
- Diverse Tech Stacks: Managing a variety of solutions across clients increases complexity.
- Limited Budgets: Many smaller MSPs operate on tight budgets, making it challenging to adopt advanced tools or expand their services. A survey reveals that 48% of MSPs reported that budget constraints limit their ability to win new business.
- Risk Aversion: Fear of disrupting existing operations prevents some MSPs from adopting new tools.
How Backup and Archiving Help:
- Standardization: Cloud-native backup and archiving streamline operations and reduce costs.
- Scalability: Flexible storage options grow with your needs, allowing MSPs to manage increasing data volumes without requiring substantial upfront costs. This ensures services can expand efficiently without adding complexity.
- Integration: Advanced solutions integrate seamlessly with other tools, minimizing the need for additional investments.
Challenge #3: Escalating Digital Threats
Cyberattacks on MSPs are rising. A 2024 report found that 76% of MSPs reported at least one cyberattack in the past year. With the expanding attack surface created by remote work and IoT, threats like ransomware, phishing, and Distributed Denial of Service (DDoS) attacks are more prevalent than ever.
Alarming Statistics:
- Ransomware: A 2023 report revealed that ransomware attacks surged by 73% compared to the previous year, with construction, healthcare, and IT services sectors being among the most affected.
- Social Engineering: Phishing attacks remain a dominant threat with significant increases in attack sophistication.
- IoT Vulnerabilities: IoT-related cyberattacks will continue to increase as the number of connected devices is predicted to surpass 75 billion globally in 2025.
How Backup and Archiving Help:
- Immutable Backups: Ensure data integrity, preventing unauthorized modifications.
- Rapid Recovery: Minimize downtime with fast restoration of critical systems and files.
Challenge #4: Compliance and Regulatory Pressures
Compliance with data privacy regulations is non-negotiable. Fines for non-compliance have skyrocketed, with GDPR penalties exceeding €2.5 billion in 2023 alone. MSPs face a constant challenge to ensure client compliance while navigating regulations like GDPR, CCPA, and HIPAA.
Common Compliance Issues:
- Data Retention: Businesses must retain specific data for mandated periods.
- Audit Readiness: Regulations require quick access to historical data during inspections.
- Tamper-Proof Storage: Ensuring data integrity is crucial for legal and regulatory requirements.
How Backup and Archiving Help:
- Regulatory Features: Tools like legal hold, retention policies, and eDiscovery simplify compliance.
- Immutable Storage: Secure archiving ensures data integrity and supports audit readiness.
- Audit Support: Rapid search capabilities save time and reduce stress during compliance checks.
The Importance of Backup and Archiving
Backup and archiving solutions go beyond operational necessity—they are strategic enablers for MSPs. By addressing data protection, compliance, and scalability, these tools empower Managed Service Providers to:
- Prevent data loss: Safeguard client information against human error and cyber threats.
- Enhance scalability: Simplify operations through automation and standardization.
- Achieve compliance: Ensure adherence to complex regulations with ease.
- Drive growth: Leverage actionable insights to boost marketing and sales.
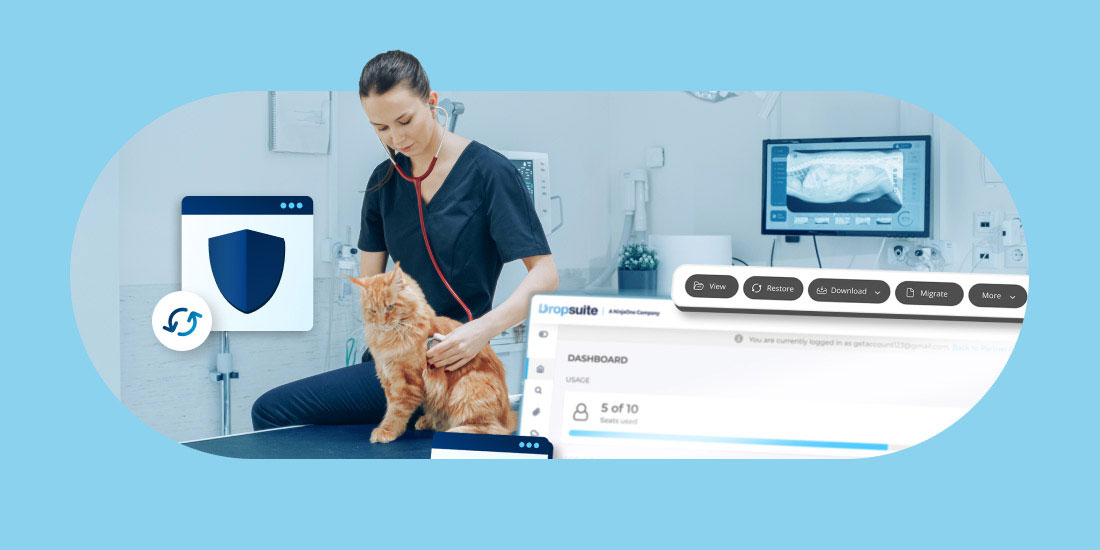
Dropsuite: Your Partner in Overcoming MSP Challenges
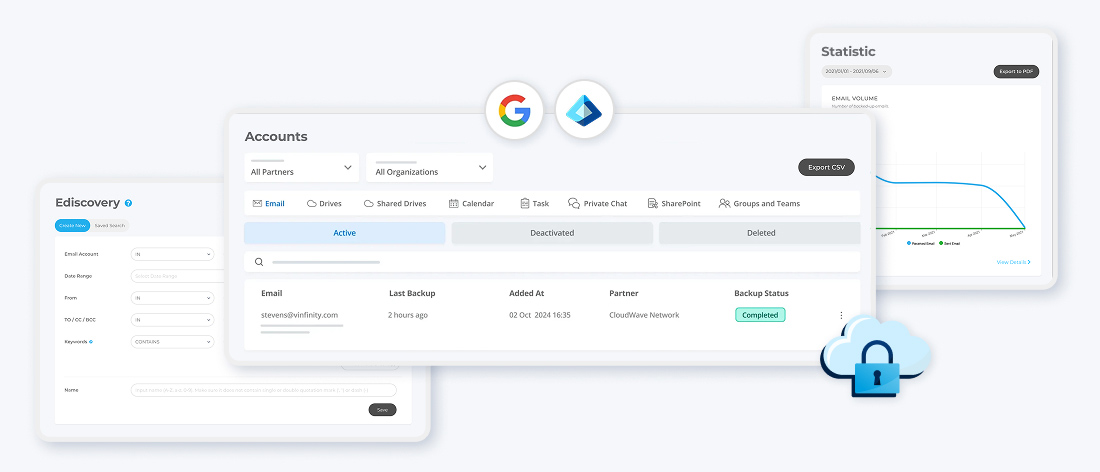
Dropsuite offers robust backup and archiving solutions tailored for MSPs, helping them tackle today’s challenges with confidence:
- Microsoft 365 and Google Workspace Backup and Archiving: Protects critical data, ensures compliance and enables seamless recovery.
- eDiscovery Tools: Simplify audits and compliance reviews with fast data access.
- Insights BI: Transform archived data into actionable insights for business growth.
Take the Next Step:
Meet challenges head-on with Dropsuite’s comprehensive solutions. Talk to our experts to learn how we can support your journey to resilience and success. Additionally, we offer MSPs access to a free trial of NFR (Not for Resale) licenses to test Dropsuite within your own organization.