Estimated Reading Time: 4 Minutes
Ransomware attacks have continuously grown in frequency. Multiple types of ransomware are popping up across various industries – and they are only getting worse day by day.
If necessary, bad actors can also find their entrance into the business’ supply chain. For some businesses that employ them, a possible point of vulnerability is their managed services providers (MSPs).
Case in point: Kaseya, an IT management software provider, announced in July 2021 that one of their remote management tools had been compromised by a ransomware threat and that customers had been hit by attacks. The damage? 50 customers were directly affected, 30 of them MSPs, resulting in more than 1,000 of their business customers getting hit with ransomware.
With this recent instance of an MSP ransomware attack, it is paramount that enterprises are aware of the various types of ransomware and how MSPs can defend themselves.
What Are the Various Types of Ransomware?
1. Crypto-malware
Differentiator: The ransomware of all ransomware. Other forms are variations on this.
2. Scareware
Differentiator: Scareware doesn’t even need to “encrypt” files – they can simply flood the screen with pop-ups and fake ads that effectively disable the unit.
3. Lockers
Differentiator: Lockers attempt to create panic and/or urgency in the target with a countdown timer to rush them into paying.
4. Doxware/Leakware
Differentiator: Most victims of these are celebrities and other public figures. Doxware is considered a form of extortion, which, in the world of cybercrime, is now big business.
5. RaaS (Ransomware as a Service)
Differentiator: The instigator of this MSP ransomware attack is not the actual hands-on attacker. Terrifyingly, this attack requires no computer coding knowledge from the original affiliate.
6. Big Game Hunting (BGH)
Differentiator: This is a low-volume, high-return attack conducted through ransomware. It is targeted, complex, and extremely different from the spray-and-pray approach that traditional ransomware has taken.
How MSPs are Affected by Ransomware
MSPs are particularly attractive targets to ransomware attackers. It’s easy to see why: gaining access to an MSPs system would open up thousands of digital doors into the various businesses that those MSPs support.
This puts the clients in danger of their data being locked up or stolen – and the MSPs in danger of reputational damage. Corruption can spread into their clients’ systems after the main network of an MSP hit with ransomware is successfully infected. A top-of-mind example would be the Solarwinds incident.
The REvil Kaseya ransomware attack was a wake-up call for an industry that relies heavily on outsourcers for support of its most critical operations. This MSP ransomware attack teaches businesses that before they choose the vendors they are partnering with, they need to step up their security vetting. That includes vetting the vendors of their vendors.
They also need to realize that the MSPs they are working with are important in planning their incident responses. Protecting MSPs from different types of ransomware should be a major priority.
“Are they [MSPs] practicing what they preach? Do they have effective security controls like MFA [multi-factor authentication] in place? Are they operating to an accepted cybersecurity framework, like NIST or CIS?” said Daniel Clayton, VP of Global Services at Bitdefender, in an interview.
“It’s important they understand what specific role they would play in an incident and, of course, that they are capable of playing that role effectively,” added Clayton. “Like any partnership, trust but verify.”
Backing Up is the Key
For an MSP previously hit with ransomware, one of the most important lessons learned is to deploy an automated, ongoing cloud-based backup solution. Even companies that are not MSPs tend to learn this the hard way.
In March of 2019, for example, Norwegian energy company Norsk Hydro suffered a ransomware attack that crippled the company’s network and stalled production in all of its manufacturing facilities. But instead of paying off the ransom, the company decided to rebuild their essential systems, like manufacturing-specific software, over the course of about three weeks. Other systems, including the company’s user directory and cloud services (which were luckily untouched), took as long as three months to bring back online. They also held a press conference to be as transparent to the public as possible regarding the attack.
Though quite noble, it did not change the fact that the hassle of rebuilding their entire system could have been reduced if they had only chosen to deploy a cloud-based backup solution. If they had, the downtime would have been significantly reduced, and recovery would have been much faster.
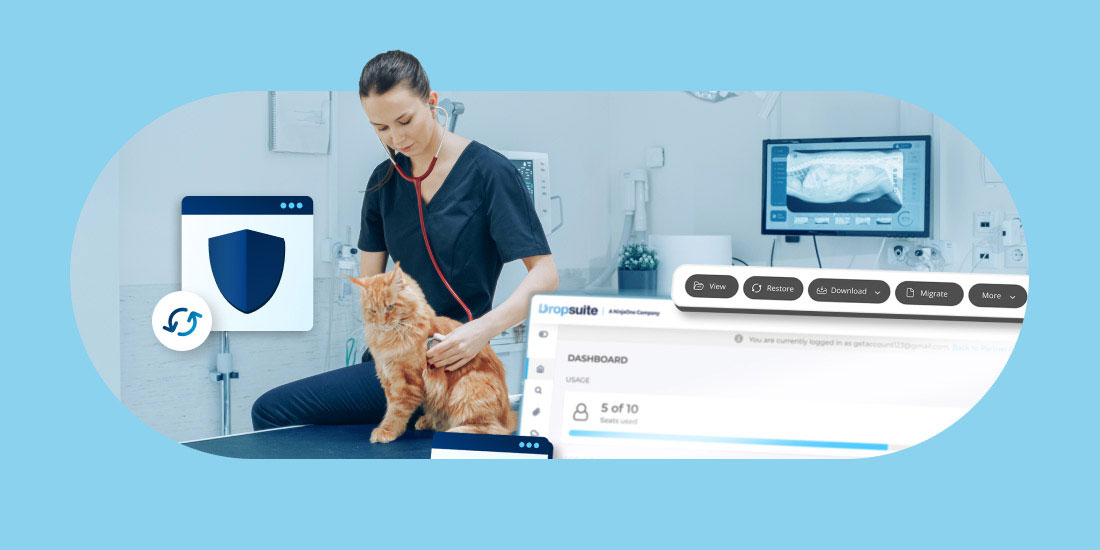
A comprehensive backup solution will maintain complete copies of your emails, attachments, tasks and calendars, work documents, websites and databases in a separate, secure system. Should an attack happen, you can restore your backed-up files easily and quickly and significantly reduce the impact of a ransomware attack.
Cloud-based backup and recovery solutions like Dropsuite reduce the impact of lost or corrupted data from various types of ransomware attacks. With Dropsuite, MSPs and their client companies can secure the following benefits:
- Automated Backup Process
Back up your Microsoft 365, Google Workspace and Email files within 5 minutes, as well as automate future backups. Incremental backups include unlimited storage and retention options to ensure you never run out of space. - Easy Administration and Management
Our admin panel with role-based access levels enables easy access granting and management. - Secure Storage
Your data is fully secured with TLS or SSL when available, and your data is encrypted using military-grade 256-bit AES. It’s protected both in transit and at rest. - 1-Click Restore and Download
Easily restore or download single files, a set of files or all files to your personal computer with the 1-Click function.
Learn more about Dropsuite and how it can help you overcome any ransomware threat.