Estimated Reading Time: 5 Minutes
Data privacy laws protect consumers and citizens from privacy violations or misuse of private data by corporations and organizations. Data privacy laws also control how companies should collect, store and utilize a citizen’s private information and govern how companies should delete or destroy data when consumers request its removal.
Managed Service Providers (MSPs) are uniquely positioned to advise clients on how to comply with various state and national data privacy laws. Moreover, MSPs are well equipped to help clients leverage technologies, policies, and procedures to ensure business compliance.
Full legal compliance is a multi-layered process, involving policies, procedures, technologies, and operational consistency, along with responsiveness and follow through when and if breaches or security incidents occur. Compliance with data privacy laws can be broken down at the highest levels into two major focuses. First, the laws require companies to implement reasonable data security measures. Next, these laws provide strict guidelines on data governance and how companies should collect, utilize, and remove consumer information, especially in response to consumer requests for data removal (a.k.a. “the right to be forgotten”).
In this blog, we will explore how MSPs can provide essential technologies and security procedures to help clients comply with “reasonable security” requirements that are foundational to nearly every data privacy law. We will explore six core technologies MSPs can deploy to ensure reasonable security.
Key Data Privacy Laws
Data privacy laws are inherently complex since most customer relationships are digital and nearly all companies can operate on a global scale. Clients should have a thorough understanding of all the geographies and jurisdictions where they operate, along with the relevant laws.
Two of the most important and far-reaching data privacy laws are the European Union’s General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA). GDPR covers the entire EU, therefore nearly any organization serving European consumers should comply. In the case of the CCPA, it protects consumers in the most populous state in the United States.
Both the GDPR and CCPA protect consumers from unlawful collection, transfer or use of their private information. Under both laws, consumers are empowered and have the right to access data that has been collected about them and under certain circumstances request that this data be removed or “forgotten.” Both laws mandate that companies leverage “appropriate” or “reasonable” data security measures to prevent breach, theft, or misuse of personally identifiable information (PII).
Protecting PII and Ensuring “Reasonable Security”
Personally identifiable information (PII) is any information that can be directly or indirectly tied to an individual. Examples of PII would include social security numbers, driver’s license numbers, credit card numbers, email addresses, phone numbers, physical mailing addresses, photos, biometric data, medical, financial, or educational information.
Protecting PII is a foundational element of data privacy laws. Organizations are required by law to prevent the theft, misuse, disclosure, or loss of PII due to security breaches or employee malfeasance. MSPs can help clients ensure “reasonableness” in their approach to data security by getting clients to adopt a widely recognized cybersecurity standard, such as the National Information Security Technology (NIST) or Center of Information (CIS) standards. These standards are far-reaching, multi-layered, and specify key technologies and procedures for full adherence to the standard. MSPs can differentiate themselves by becoming experts in these standards and engaging clients with consulting and services to help drive client adoption and compliance.
Specifying what should be done is only half the battle. Far too commonly, organizations will adopt a strict security standard and set the bar high on their policies and ambitions, and then fail to follow through with execution and enforcement. Strict adherence and follow-through can be challenging if a company culture biases “getting stuff done” over “doing it right.” MSPs can play a vital role by ensuring operational follow-through on security procedures, best practices and technology implementations. Fortunately, complying with a standard and implementing sound security practices is not just the law, it is also a good business practice.
6 Core Technologies for MSPs
Here are six core technologies MSPs can deploy to help clients protect PII and implement reasonable and appropriate security measures.
1. Identity and Access Management (IAM)
IAM is the process of making sure the right people have the right access to the right resources (applications or data) inside an organization. Sound IAM practices are essential to ensure employees access and utilize PII correctly. IAM ensures that logs are created to track access to various forms of PII and other sensitive information. IAM technologies prevent hackers and cybercriminals from accessing unauthorized systems, software tools, or other information such as PII. IAM processes should also leverage Multi-factor Authentication (MFA). Expert Insights lists their Top 10 IAM Solutions.
2. Encryption
Encryption is necessary across a whole host of software systems, databases, and endpoint devices. Encryption ensures that if data is lost or stolen, it won’t result in a breach of PII. Encryption should be used for data in motion and data at rest. Full disk encryption should be used for laptops that may contain PII in use by remote workers or on-the-go professionals. ZDNet offers their picks for best encryption software for 2022.
3. Mobile Device Management (MDM)
MDM technology enables organizations to protect and govern company information that often resides on employee mobile devices, such as smartphones or tablets. Most commonly today, employees bring their own devices (BYOD) to their daily work, yet nearly all these devices access corporate systems such as email, file collaboration platforms, or other apps that likely contain PII or other sensitive corporate information. MDM technology allows companies to monitor, control, or delete company data, PII, or applications from mobile devices, especially if the device has been lost or stolen, which is incredibly common. Here are TechRadar’s best MDM solutions in 2022.
4. Email Security
When folks think about email security, they often think about spam and phishing defense. Keeping unwanted or dangerous emails out is certainly the common goal of an email security platform. However, just as importantly, email security systems should be used to provide outbound security as well. Email security systems can be configured to detect and block the unauthorized transmission of PII by email by employees or cybercriminals who may have breached a corporate email system. If left unprotected, email systems can be used to steal or exfiltrate vast quantities of customer information. Fortunately, email security systems have the ability to filter and control outbound emails and block the authorized transmission of PII. Cyber Security News gives their Top 10 Email Security Solutions.
5. Data Loss Prevention (DLP)
DLP technology is similar to outbound email security. DLP technology defends against the mass exfiltration of data by employees, hackers or cybercriminals. DLP technology can also simply govern the movement of data inside an organization and its software systems, for instance, by preventing employees from moving sensitive information from a server or cloud repository to a mobile device or laptop. DLP acts as a global data traffic cop, preventing data from moving where it shouldn’t. DLP technology is vital for the protection of PII, company trade secrets, financial information, or other intellectual property. Software Testing Help provides the Top 11 DLP solutions in 2022.
6. Backup, Disaster Recovery, and Data Retention
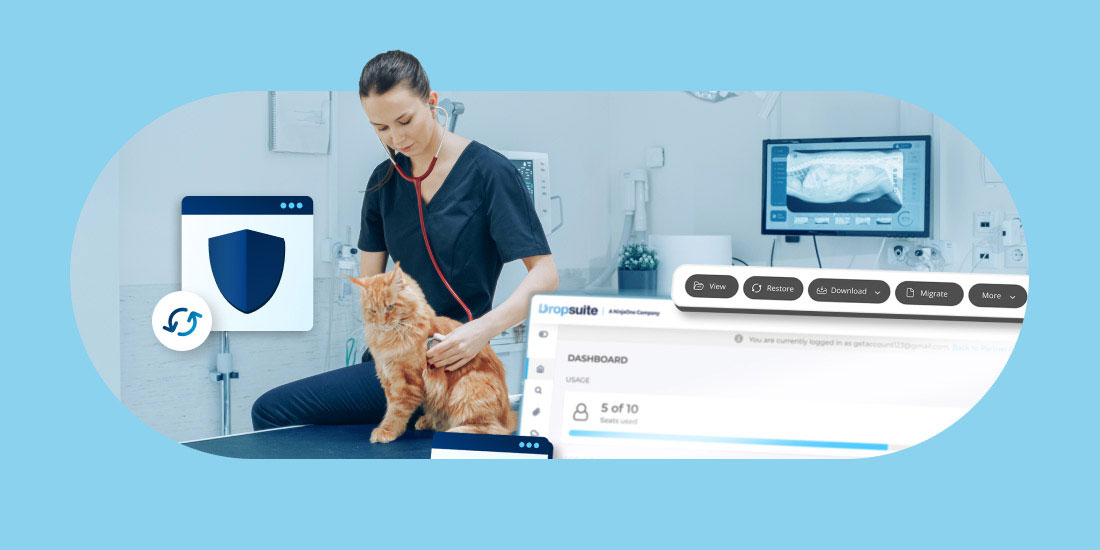
A company’s backup strategy is often overlooked when considering how to comply with privacy laws. Not surprisingly, privacy governance laws specify that organizations should have reasonable backup and recovery procedures, just like they should have reasonable security procedures. For example, GDPR stipulates “the ability to restore the availability and access to personal data in a timely manner in the event of a physical or technical incident.” Therefore, companies should have in place robust backup and recovery procedures that enable them to recover from a wide range of business disruptions. What’s more, organizations need advanced backup technology that enables the complete deletion and removal of private data, when requested, from production systems and all backups.
Backups cannot be chaotic and poorly maintained, since situations may arise where consumer requests to delete data may occur in production systems but remain in poorly maintained backup systems. Therefore, MSPs need state-of-the-art backup and recovery systems that enable compliance with relevant privacy laws. SaaS solutions like Dropsuite’s Email Archiving offer features like journaling, permissions and advanced search to ensure compliance with data privacy laws.
Conclusion
Dropsuite helps organizations and managed service providers backup and protect SaaS-based data and content from applications such as Microsoft 365 and Google Workspace. As we have explored in this blog, advanced backup and recovery technologies are critical to enable MSPs to help companies comply and thrive in our digital economy.