Estimated Reading Time: 3 Minutes
Table of Contents
In the evolving landscape of cybersecurity, Managed Service Providers (MSPs) play a crucial role in educating and protecting businesses against growing threats. Among these, spear phishing remains one of the most insidious and damaging types of cyberattacks. This highly targeted form of phishing leverages personalized tactics to deceive victims into divulging sensitive information or engaging in fraudulent activities.
For MSPs, understanding the nuances of spear phishing and equipping clients to combat these attacks is essential. This blog explores the realities of spear phishing and actionable strategies to mitigate its impact.
What is Spear Phishing?
Spear phishing is a targeted attack designed to steal credentials, execute financial fraud, or compromise systems. To define spear phishing simply, it’s a phishing method that focuses on specific individuals. This is key in understanding spear phishing vs phishing: while standard phishing casts a wide net, spear phishing attacks are carefully crafted to manipulate particular victims – often executives or employees with access to critical systems.
For example, a mid-level finance employee may receive an email impersonating their CFO, urgently requesting a wire transfer. Similarly, attackers may impersonate vendors or partners to extract credentials or sensitive information from that mid-level finance employee. These spear phishing examples illustrate how attackers exploit trust within organizations.
Key Stats:
- Spear phishing emails make up less than 0.1% of all emails sent yet cause 66% of all breaches.
- According to one study, Business Email Compromise (BEC) scams (a type of phishing attack) were responsible for only 4% of breaches but had an average cost of $5.01 million per breach to businesses.
How Do Spear Phishing Attacks Differ from Standard Phishing Attacks?
Spear phishing attacks are highly customized, using social engineering to bypass traditional security measures. Cybercriminals often:
- Research Targets: Attackers may scour social media profiles, company websites, or even past email threads to craft believable messages.
- Avoid Links or Attachments: Unlike traditional phishing, spear phishing emails may contain no detectable malicious elements, making them harder to flag by spam filters.
- Exploit Trust: By impersonating trusted colleagues, executives, or vendors, attackers exploit inherent trust in internal communications.
For MSPs, traditional email security solutions often fail to detect these attacks due to their bespoke nature. Investing in AI-driven email security tools can be useful in identifying anomalous behavior rather than relying solely on signature-based detection.
Why is Spear Phishing the Most Harmful?
Spear phishing attacks are not only sophisticated but also financially and operationally devastating. They often target:
- C-level Executives: Research indicates that 72% of C-suite executives have been targeted by cyber-attacks, yet 37% of firms do not offer additional cyber protection for them.
- IT Administrators: Cybercriminals frequently target IT staff to gain control over infrastructure and execute ransomware or lateral movement attacks.
- Finance Teams: Employees in accounts payable or payroll departments are prime targets for fraudulent wire transfer requests.
The consequences can include direct financial loss, data breaches, reputational damage, and compliance violations.
How Does Spear Phishing Impact MSPs?
For MSPs, spear phishing creates a twofold challenge:
- Increased Workload: Responding to phishing incidents is resource intensive.
- For IT and security teams, dealing with the threat of a single phishing email takes an average of 27.5 minutes at a cost of $31.32 per phishing message.
- IT and security teams spend 33% of their total available time handling phishing threats every week.
- Client Trust: Failure to prevent or respond effectively to spear phishing incidents can damage client relationships and confidence in MSP services.
What Can MSPs Do to Combat Spear Phishing?
MSPs can implement a multi-layered approach to tackle spear phishing effectively:
a. AI-Driven Email Security
- Deploy email security solutions that use machine learning to detect anomalies in message behavior, sender patterns, and content tone.
- These tools excel at identifying subtle red flags, such as domain spoofing or context mismatches, that traditional filters miss.
b. Multifactor Authentication (MFA)
- Enforce MFA across all systems. Even if credentials are compromised, MFA adds an additional layer of protection to prevent unauthorized access.
- Deploy MFA universally, particularly for email accounts, financial systems, and privileged accounts.
c. Cybersecurity Awareness Training
- Build a human firewall by educating employees to recognize phishing attempts.
- Incorporate phishing simulations into training programs to test employee responses and create teachable moments.
d. Financial Controls
- Implement strict financial processes requiring multiple sign-offs for large transactions.
- Set thresholds for wire transfers or ACH payments that trigger mandatory reviews.
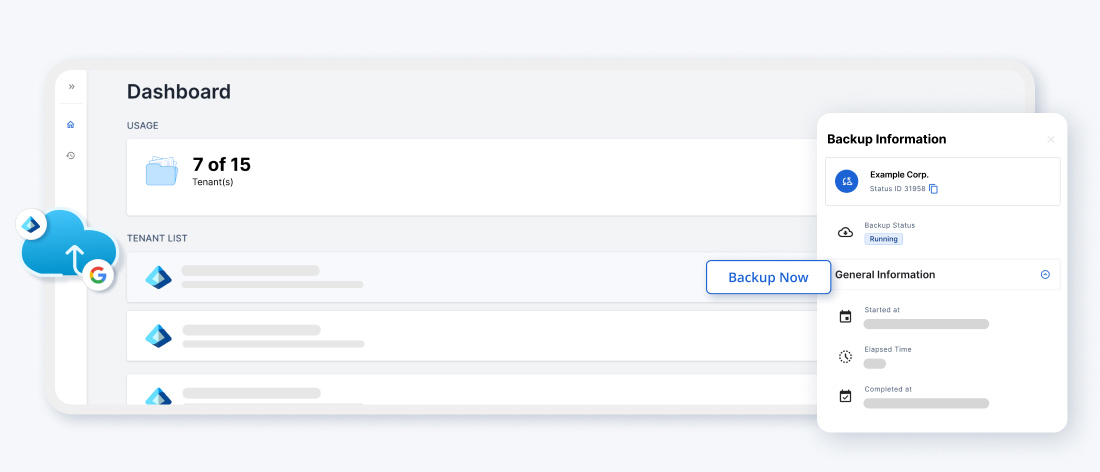
e. Backup and Recovery Solutions
- Equip clients with robust email backup and archiving solutions. Backups ensure business continuity even if an account is compromised or data is deleted.
- Dropsuite enhances this with Entra ID Backup, which protects essential identity configurations like user profiles, M365 Groups, and roles. By offering automated, incremental backups and fast, precise recovery options, MSPs can ensure seamless identity management while minimizing downtime caused by misconfigurations or cyberattacks.
- Dropsuite provides MSPs with tools to back up, recover, and archive business-critical emails, forming a reliable defense against data loss.
Why MSPs Must Take the Lead
MSPs are uniquely positioned to help clients defend against spear phishing by:
- Delivering education and training to build awareness.
- Offering advanced security solutions that combine technology with proactive monitoring.
- Establishing best practices for data protection and implementing backup and recovery as part of a comprehensive business continuity plan.
By addressing spear phishing as a strategic priority, MSPs can reduce the risk of incidents and strengthen client trust.
Protect Against Spear Phishing with Dropsuite
At Dropsuite, we empower MSPs with tools to combat the growing threat of spear phishing. From robust email backup and recovery to advanced archiving and compliance features, Dropsuite helps MSPs build resilient defenses for their clients.
Ready to protect your clients?
Contact us today to learn more or try Dropsuite for free.