Estimated Reading Time: 4 Minutes
Ransomware is on the rise. Approximately 500 million ransomware attempts were recorded in 2021 – a 148 percent surge compared to the previous year.
Unfortunately, the nefarious success of ransomware means that more and more bad actors want to cash in. Ransomware is now a lucrative business, and as a result, a black market of attackers has sprung up. Hence the rise of Ransomware-as-a-Service (RaaS) – the emergence of bad actors-for-hire that rent out their ransomware expertise to attack people and businesses.
What is RaaS? How did it become a booming business? And, crucially, how can MSPs protect themselves from it?
What is Ransomware-as-a-Service?
RaaS is a nefarious creation of the cybercriminal market – sold for people and parties that want to perform ransomware attacks, but lack the time, the tools, and the expertise to do so.
This ransomware-as-a-service business model has two main parties involved: the hacker and the “affiliate”.
The affiliate is the one who initially requests the attack and reaches out to a professional hacker to perform it. The hacker carries out the attack and, if successful, will receive a share of the ransom in exchange for their services.
The RaaS business model benefits both parties in more ways than one: the affiliate gets what they want with a successful attack, and the hacker can focus on developing their products further. It also falls on the affiliate to find the “victims” so that the ransomware developer can concentrate on discovering more ways to infect more people and increase their profits.
For this system to work, developers generate a specific code with a unique, embedded identifier within the ransomware. This code is connected to their affiliate, and it splits the payout between the two parties that infected the victim.
An Illegally Lucrative Business
Ransomware-as-a-Service groups can create massive damage and position themselves for multi-million dollar demands using complex and sophisticated techniques. They use attack sequences similar to advanced persistent threats (APTs) – stealthy threat actors that gain unauthorized access to a computer network, remaining undetected for an extended period of time. This allows for more persistence, enabling lateral movement across the network and data exfiltration for double extortion.
Reports indicate that the average cost to remedy a ransomware attack has “more than doubled, from $761,106 in 2020 to $1.85 million in 2021.” Moreover, it is predicted that by 2031, the total cost of ransomware payouts would likely amount to about $265 billion.
Some examples of RaaS groups and platforms are Cerber and REvil (also known as Sodinokibi).
In 2016, Cerber was named the largest RaaS ring, consisting of “161 active campaigns with eight new campaigns launched daily.” It was also estimated that the group earned close to $200,000 in just a single month that year, which brought their annual earnings to a whopping $2.5 million.
REvil developers’ claim to fame, on the other hand, was allegedly making over $100 million within a year, attributing their “success” to focusing on targeting large businesses. They’ve also made known their desire to make $2 billion from their RaaS platform before they close down shop. The group went dark in July 2021, but have since resurfaced in September.
Ransomware-as-a-service teams can target their own as well, which the REvil team did as they came back.
Stories of REvil taking over other threat actors’ negotiations surfaced, as multiple APT groups began talking amongst themselves on underground forums. This has been happening since 2020.
A Security Boulevard article reports that REvil developers “would inject themselves into negotiations with an affiliate by posing as the victim and claiming that they had decided to not pay. They would then open a second chat with the victim and collect the ransom without the affiliate’s knowledge, thus entitling them to keep the full payment for themselves.”

5 Key MSP Cybersecurity Threats of 2022
Highly Professional, Highly Illegal
Abnormal Security, an email security provider, discovered that few of their customers’ staff received emails that invited them to “install ransomware on a company computer in return for a $1m share of the ‘profits’.”
Such Ransomware-as-a-Service “packages” exist on dark web forums, which offer scalable, easy-to-use toolkits. Developers of said packages have also increasingly become highly professional. They have started offering additional incentives and services like bulk discounts, 24-hour support, user reviews, discussion forums, and more. These “services” are noticeably similar to what legitimate SaaS products would offer.
According to Mitch Mellard, principal threat intelligence analyst at Talion:
“The store pages are almost disturbingly corporate. Using the example of the page for the EGALYTY ransomware-as-a service, they proudly display links to online infosec publications specifically discussing their strain like a badge of honour, like a mundane software store would display positive reviews from tech publications.
They then display a multi-tiered service list, ranging from a one-month ‘test’ package for $90, proceeding to ‘standard’ and ‘premium’ offerings, before arriving at the 12-month ‘elite’ subscription package, with all of the bells and whistles, for $1,400.”
Disturbing news, indeed. But this just highlights the importance of now having the right protocols to protect one’s business from RaaS attacks.
Protecting Your MSP Against RaaS
Any business, especially MSPs, can take steps to mitigate ransomware-as-a-service attacks. This requires a multilayered approach that will improve your network’s overall security. TechTarget lists the following six key steps to safeguard assets against ransomware risks:
- Have a multi-layered, in-depth security system to defend your business not only against ransomware attacks, but also against other digital risks and threats.
- Solutions that have extended detection and response capabilities can help in identifying potential risks that ransomware attackers can exploit
- Educate your employees on social engineering and ransomware risks. Establish an official list of the dos and don’ts of using your communication technologies.
- Keep your software and firmware patched and updated regularly.
- Use tabletop exercises to keep your employees prepared on how to respond to ransomware attacks. This will also help discover potential gaps and vulnerabilities in your response protocols.
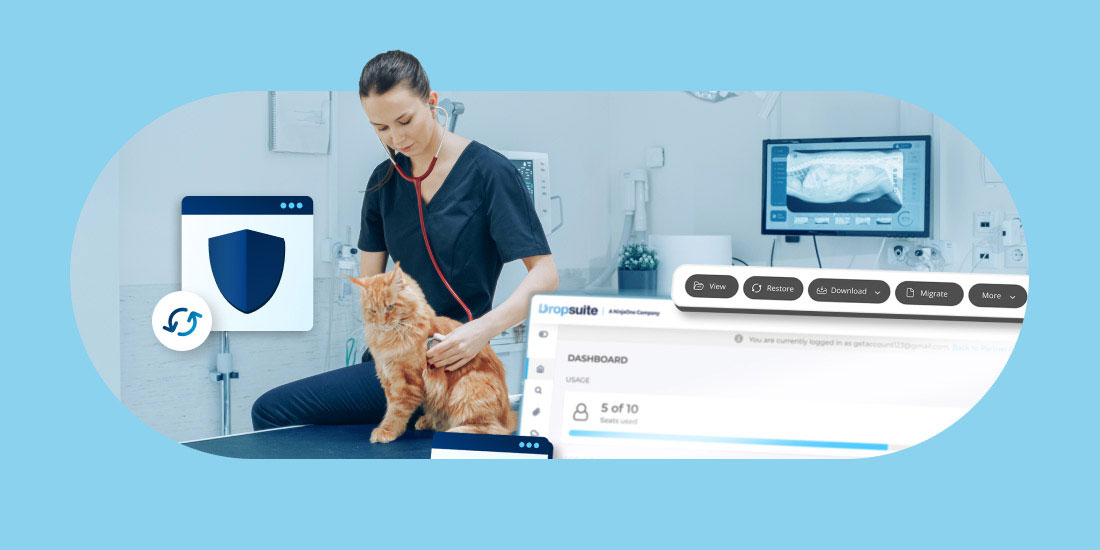
- Back up your data as frequently as possible. With reliable backups, the risks of data loss is mitigated/minimized.
Disturbing news, indeed. But this just highlights the importance of now having the right protocols to protect one’s business from RaaS attacks.
These steps are solid. However:
Backing up is especially important on two fronts: one, as a pre-emptive action to ensure that you have your data securely backed up in case of attack; and two, to facilitate speedy recovery in case of a successful attack from ransomware-as-a-service groups and platforms.