Most online retailers aren’t large corporate enterprises like Amazon, Alibaba, eBay, or Rakuten. They aren’t even as big as Brayola (who sells bras) or Harry’s (who sells shaving supplies), and you’ve probably never heard of these last two. Most e-commerce companies are small, family run operations who have carved out businesses for themselves by offering the right subset of products to the right niche audiences.
The largest e-commerce brands have deployed rigorous security, at all levels throughout their organizations, to keep their businesses from harm. Smaller companies have the same requirements but often cannot afford or simply choose to overlook the threats that their electronic businesses face.
The 2015 Information Securities Breaches Survey, commissioned by Ed Vaizey, Britain’s Minister for Culture and the Digital Economy, stated that the cost of security breaches has increased greatly. The average cost to a large organization jumped from £600k – £1.15m in 2014, to £1.46m – £3.14m in 2015. The average cost for small business increased from £65k – £115k in 2014, to £75k – £311 in 2015, with the higher end more than doubled.
Australian Prime Minister, Malcolm Turnbull stated during the launch of the nation’s Cyber Security Strategy that the annual cost of cybercrime to Australia amounts to more than A$1 billion in direct cost, with some estimates placing it about A$17 billion, almost as high as one per cent of annual GDP.
Most security experts would agree that the world is wrestling with a huge cyber security problem that cannot by defeated, but can only be mitigated with concerted effort applied to defending one’s business.
Security professionals often say that they don’t like promoting best practices — or a checklist method of explaining things — because “one size does not fit all.” While this may be the case, there is a reason they are called best practices — when employed, a best practice can put you in a much better place than where you started without the expert guidance. Let’s examine the checklist further.
A 5 Point Website Security Checklist for E-commerce Retailers
- Backup & Redundancy
- PCI Compliance
- Encryption
- DDoS protection
- Firewalls
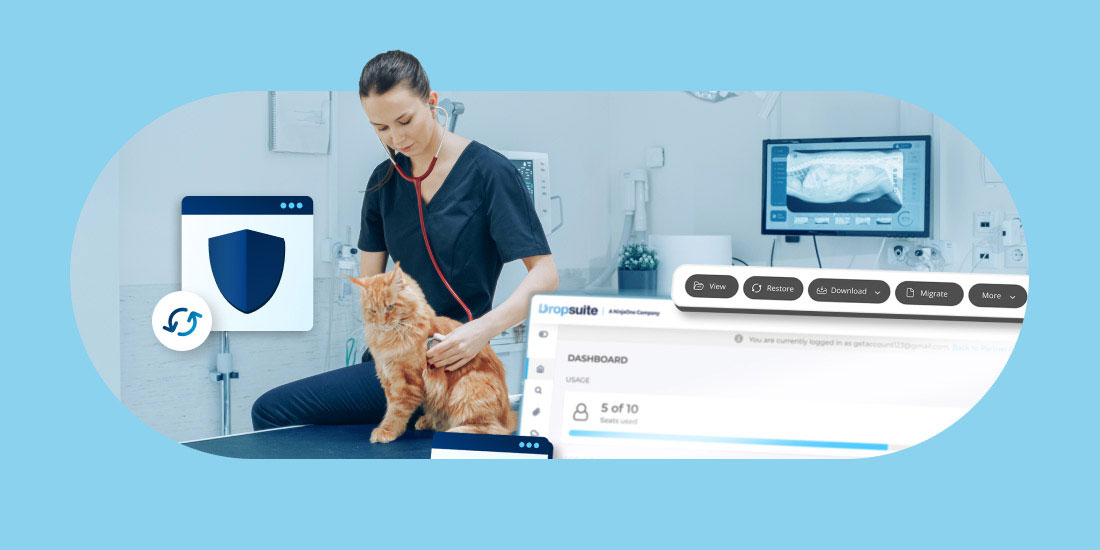
1. Backups & Redundancy
Why is backup first? That’s easy.
When you start writing a Word document and you are 100 words in, what do you instinctively do? You save it. That’s because we’ve all been there; two pages in and then tragedy strikes! The Blue Screen of Death on Windows or the endless spinning rainbow on a Mac. Whether you are coding a website or doing some design work, busy professionals have learned the importance of backing everything up, repeatedly and rigorously.
Here are some tips. Start from a safe, secure and redundant place. That way, no matter what happens, your most important assets — your data — and the most valuable thing you own — your time — are not wasted when your computer malfunctions.
You can plug in a storage device into your computer or mobile phone and manually backup your data onto a physical devise. This is a good start, but it’s kind of a pain to do and it’s not always the least expensive way to perform critical backup. And since your physical device is sitting there next to you, if you have a catastrophic fire or a theft, there goes your data!
There a plenty of cloud-based backup options for you to choose from — from email archiving to automated website backups to ensuring that your business servers are protected from harm with products like DSE Server Backup from Dropsuite. Many hosting providers offer great cloud backup solutions as well.
Don’t sell yourself short. Set up a data backup solution — or use more than one — as soon as you can. Gain instant peace of mind and protect your e-commerce business assets.
2. PCI Compliance
What’s PCI compliance? Well, if you just started selling online, you may not be aware of this. Most likely, if you are using a payment provider like Stripe or Square, you are already in the PCI Compliance world.
The PCI Security Standard Council is an international best practices group for payment account security. The have set up and continue to develop security standards in the area of online payments and if you are accepting Visa, MasterCard, Discover or American Express, then you must adhere to the PCI DSS: an acronym for the Payment Card Industry Data Security Standard.
The most common way to adhere to these standards and reduce PCI scope is by following the tokenization method. According to the PCI Compliance Guide:
“Tokenization eliminates electronic card holder data (CHD) from being stored in your environment. This means you do not need to focus as much on the storage and retention of your customers’ CHD; however, keep in mind you still need to review and assess how it is transmitted and processed.
This means that your shop workers, sales staff and third parties don’t have to deal with payment information — and so you don’t have to safeguard them or think about the consequences of financial data going rogue.
Of course, of critical importance will be ensuring the payment processors you use are water-tight. You’ll need to make sure they are compliant with the PCI DSS (you should require that they permit you to visit their facilities and meet with their staff who manage the tokenization function to fully explain to you how it works). This is your customers’ CHD and while your scope has been reduced significantly by using tokenization, it is still your responsibility to ensure the vendor you choose to use is sufficiently safeguarding it all.”
Being PCI compliant greatly reduces your exposure to potentially catastrophic incidents related to card holder data being lost, stolen or abused. It also gives your e-commerce clients greater peace of mind when doing business with you.
3. Encryption
If you hadn’t heard of encryption much in the past, it’s guaranteed that you have heard of it more recently in the news. From Edward Snowden to Apple and the FBI, encryption is in the news. When talking about your e-commerce website and your data — and even more so, your customers’ data — encryption is your friend. It is what allows us to send private information, like card data or client identifiers across the web without anyone else seeing it in transit while it’s being sent.
– Login pages should be encrypted
Encryption should happen anytime details are being entered into a form (live chat, order forms, logging into a customer account, etc). More often than not — and it’s a bit worrisome really — most online retailers only encrypt data AFTER the login details have been entered. Using a SSL after user authentication is like locking the door but leaving the key hanging outside after you go in. So encrypt in front of the login too.
– Data transmissions should be encrypted
Whether for backup or for website management, always use encrypted protocols — like SFTP instead of just FTP, and HTTPS instead of just HTTP, and SSH with a secure tool like OpenSSH.
It would be wise to point out at this point, if you are using public WiFi, at the very least use a VPN (virtual private network).
4. DDoS Protection
There are many tools and services out there to protect e-commerce businesses against DoS (Denial of Service) and DDoS (Distributed Denial of Service) attacks. Foremost among them is the 800lb free tool, CloudFlare. Not using a DDoS protection is like going cage diving with Great White Sharks, but within being locked safely behind a steel cage. Not wise.
5. Firewalls
Firewalls, whether utilizing hardware or software, work by allowing or disallowing traffic, based on what you’ve authorized. It’s something like a wall. It protects your business by blocking unauthorized traffic and possibly malicious internet traffic from accessing your network or system. There are number of different firewalls but the ones you should consider for your website are application gateways and proxy firewalls.
– Application Gateways
According to Techopediaii, “an application gateway or application level gateway (ALG) is a firewall proxy which provides network security. It filters incoming node traffic to certain specifications which mean that only transmitted network application data is filtered. Such network applications include File Transfer Protocol (FTP), Telnet, Real Time Streaming Protocol (RTSP) and BitTorrent.”
This gateway would sit on the client and server firewall. It conceals IP addresses and other information that should remain secure for the client. “The application gateway and external computer function without client information or knowledge of the proxy server IP address.”
– Proxy Firewalls
A proxy firewall acts like a middleman between on premise clients and outside servers. On top of monitoring and intercepting internet request/responses, a proxy firewall also screens incoming traffic for Layer 7 protocols: this is the application layer where most protocols, including FTP, SMTP, POP, HTTP and DNS, interact with each other. A proxy firewall can use different technologies to recognize incoming attacks.
Proxy firewalls are considered the best kind of firewall because they can fully prevent direct network access to other internal systems. This is because a proxy firewall has its own IP, and any traffic that an outside server would see would never see the true originating IP within the network since it was passed through the firewall. The only drawback is that it can be slow due to the extra connections that are being established for each packet.
Summary
The 5-point “best practices” checklist we’ve just outlined above can definitely benefit your e-commerce business by increasing the security of your data. Backup, PCI compliance, encryption, DDoS protection and firewalls can greatly reduce your risk of catastrophic system failures or cyber attacks, and in some cases, can completely eliminate the smaller issues before they grow into catastrophic business losses.
If you manage an unsecure e-commerce website, the success of your business may go down drain when something bad happens. And it’s not a matter of if, but when.
By keeping up to date on data security and backing up your assets regularly, you and your e-commerce business will be safe; your customers will feel more secure; and you will have a much greater chance of having a successful and long running online business.